What is Happening
Since the end of 2025, Bastion has observed a sharp increase in the volume of malicious Chrome extensions which are secretly harvesting AI conversation data and browsing activity.
Threat Actors are leveraging the rapid adoption of AI tools by developing malicious Chrome extensions with these functionalities. The extensions Bastion have identified appear legitimate at face value and are accompanied by thousands of downloads and positive reviews. However, the underlying code of the Chrome extensions displays malicious intent or is operating in a grey area of regulatory compliance.
When was the last time you clicked “Add to Chrome” without understanding the risks?
Bastion has identified three malicious chrome extensions which are operating as malware:
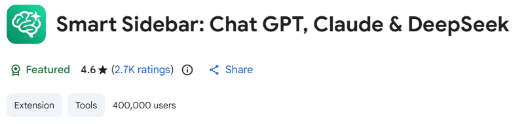
- Chat GPT for Chrome with GPT-5, Claude Sonnet & DeepSeek - Version: 1.9.6 - with over 400,000 users (ID:fnmihdojmnkclgjpcoonokmkhjpjechg)
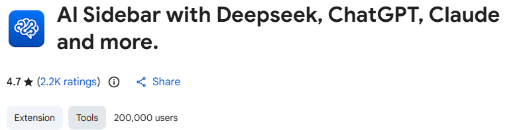
- AI Sidebar with Deepseek, ChatGPT, Claude, and more - Version: 1.6.1 - with over 200,000 users (ID: inhcgfpbfdjbjogdfjbclgolkmhnooop)
- Urban VPN Proxy - Version: 5.11.6 - with over 26,000,000 users (ID: eppiocemhmnlbhjplcgkofciiegomcon)

These Chrome extensions remain publicly available on the Chrome Web Store at the time of writing.
How Does It Work
The malicious Chrome extensions identified in this campaign are abusing the level of privileges a user provides when they click “Add to Chrome”. The extensions are published as AI productivity helpers, AI sidebars or VPNs which function as you would expect them to and are unsuspecting to the end user as they have high download counts and positive reviews. Bastion has observed the tools requesting over privileged permissions such as “Read and change all data on all websites”.
Allowing these permissions provides the extension to capture extensive AI conversation data such as user prompts, responses and meta data from the webpage’s DOM file. It also captures browsing activity data such as complete URLs, search terms and user IDs which are all fed back to the threat actor’s servers.
The potential level of compromise can likely be significate to your environment if AI tools are heavily relied upon or exist in shadow IT due to data being exposed such as:
- Sensitive Internal Documents or Communications
- Personal Identifiable Information (PII) of internal employees
- Session Tokens and User ID’s
- Internal Corporate URLs
This information is immensely valuable to threat actors and can be weaponised for attacks such as spear phishing campaigns or corporate extortion.
What Can You Do
- Review current browser extensions across your environment for unsanctioned usage
- Block browser extensions by default, unless there is a legitimate business requirement
- Implement restrictive group policies or application controls accordingly within your environment
- Conduct Security awareness training on the risks of third-party browser extensions
- If these known impacted browser extensions have been detected in your environment
- Uninstall immediately, group policy will disable extensions but not uninstall them
- Initiate password resets and revoke session tokens for impacted accounts after uninstallation
- Delete all cookies and browsing data
For further information on how Bastion can protect your organisation from these types of attacks, please contact your account manager or info@bastionsecurity.co.nz for further information.
Bastion is committed to protecting our customers from cyber threats and ensuring business continuity. If you have any questions or concerns about the above attacks, recent exposures or potential impact to your IT systems, please reach out.


























