Introduction:
PHP is a widely used open source programming language that runs on web servers and is used to build and manage dynamic websites and online services. It allows websites to process data, handle user input, and generate content in real time.
During a security engagement, Conrad Draper discovered a stored Cross-Site Scripting (XSS) vulnerability in the PHP-FPM status endpoint which was due to a lack of input sanitisation of the request URI. This affects the request URI when displaying stored content within the status endpoint.
The vulnerability affects PHP version up to 8.5.6, was assigned CVE-2026-6735 and has a CVSS score of 5.7.
This post outlines the technical details of this vulnerability, how it can be exploited, and the potential impact to users.
The Vulnerability:
When rendering stored content within the FPM status endpoint, content within the request URI was vulnerable to injection due to insufficient sanitisation.
Any unauthenticated individual could craft a malicious payload to perform XSS or potentially inject malicious XML nodes within the vulnerable site.
An attacker does not require authentication or access to the status endpoint, but may simply visit a URI embedding the malicious code.
The following screenshot shows an unauthenticated user navigating to a non existent web page to embed code within the status endpoint:
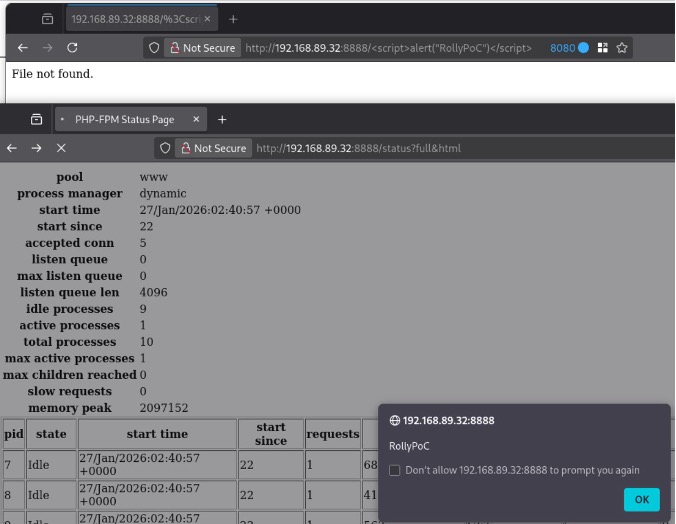
Navigating to /status?full&xml would display an XML rendering error, potentially allowing for malicious XML nodes to be injected.
The vulnerability affects PHP-SRC < 8.5.6
Disclosure Timeline:
January 27th, 2026: Issue reported to PHP.
April 21st, 2026: Followed up regarding remediation.
April 21st, 2026: PHP acknowledged & created patch.
April 21st, 2026: CVE-2026-6735 assigned.
May 8th, 2026: Advisory Live & patch published.
References:
XSS within PHP-FPM status endpoint:
https://github.com/php/php-src/security/advisories/GHSA-7qg2-v9fj-4mwv
PHP 8 ChangeLog 8.5.6:
https://www.php.net/ChangeLog-8.php#8.5.6
PHP-SRC Releases:
https://github.com/php/php-src/releases

























